Wednesday 7 January 2009
OpenSSL vulnerability
There is a new vulnerability in OpenSSL in all versions prior to 0.9.8j, discovered by Google's security team. You will be happy to learn that the Grid PKI is not affected by the vulnerability since it uses RSA signatures throughout - only DSA signatures and ECDSA (DSA but with Elliptic Curves) are affected. (Of course you should still upgrade!)
Monday 5 January 2009
New MD5 vulnerability announced
In 2006 two different MD5-signed certificates were created. A new stronger attack, announced last Wednesday (yes 30 Dec), allows the attacker to change more parts of the certificate, also the subject name. To use this "for fun and profit" one gets an MD5 end entity certificate from a CA (ideally one in the browser's keystore), and hacks it to create an intermediate CA which can then issue anything. Browsers generally accept this because then they trust the root and accept that the client sends an intermediate CA which the browser doesn't know about.
The IGTF's Risk Assessment Team (RAT) worked over the new year to analyse the threat and its implication for the Grid, including other attacks not proposed in the vulnerability announcement. The IGTF issued a statement about the vulnerability of the Grid. Essentially, CAs are trusted explicitly on the Grid (installed in/etc/grid-security/certificates) and the Grid is much less vulnerable than commercial PKIs (plus we have no CAs issuing MD5-signed end entity certs).
Note that while the Grid is not directly vulnerable, it is still possible to attack the Grid indirectly via the original proposal: e.g. if you fool the browser into thinking you're a trusted portal with a certificate from a commercial CA, and then you steal passwords such as MyProxy credentials.
The IGTF's Risk Assessment Team (RAT) worked over the new year to analyse the threat and its implication for the Grid, including other attacks not proposed in the vulnerability announcement. The IGTF issued a statement about the vulnerability of the Grid. Essentially, CAs are trusted explicitly on the Grid (installed in/etc/grid-security/certificates) and the Grid is much less vulnerable than commercial PKIs (plus we have no CAs issuing MD5-signed end entity certs).
Note that while the Grid is not directly vulnerable, it is still possible to attack the Grid indirectly via the original proposal: e.g. if you fool the browser into thinking you're a trusted portal with a certificate from a commercial CA, and then you steal passwords such as MyProxy credentials.
Thursday 18 December 2008
IGTF release 1.26 annotated
Folks, you probably saw the announcement, the new distribution came out of IGTF Sunday.
Overall the release is not urgent. I meant to send out an evaluation earlier but ran out of time.
--jens
Annotated changes:
* Added accredited classic Indian Grid CA (IGCA) (hash da75f6a8) (IN)
Good for those folks over in Cambridge working on EUIndiaGrid. INFN
no longer has to be the catch all.
* Updated IUCC root certificate with extended life time (IL)
Israel: they recently went through a self audit and I need to review this audit, I've been remiss (I was assigned as a reviewer). They re-signed their certificates to extend the lifetime (previously till summer 09) and fix some bugs. It is still the same public key but the fingerprint will have changed. Unfortunately they introduced some more minor problems...
* Updated BEGrid (web, CRL) and UCSD-PRAGMA (web) URL metadata (BE, AP)
These are just the .info files.
* New BEGrid2008 root certificate (transitional) (BE)
Old one due to expire end of Feb 09, and it's still in there. Belgium may call the new one transitional(?) but its lifetime is 10 years.
Now here's the rub. If the old one expires in Feb, and the new one is created just now, what signed the existing valid certificates?
* Extended life time of the SEE-GRID CA (SEE)
Again using the same key as before, the lifetime of the existing certificates has been extended from expiring August 09 to August 2014. This is normally "harmless" except for the Mozilla NSS bug where a browser gets confused if it sees a different version of the "same" certificate at the remote end. They did in fact keep the same serial number, so they will get this problem. (Sometimes you can change the serial, sometimes not - another long story.)
"SEE" by the way is South Eastern Europe. Another EU thing. (www.see-grid.org, FP6 funded project)
* Included CRL for NCSA SLCS CA (US)
This was subject of a (yet another) long discussion. (In the world of grid certificates, long and heated is the norm for a discussion.)
The simple version is that SLCS is Short Lived Credential Service. They should not need to issue CRLs, since short lived credentials by definition live short lengths of time. However, much of the middleware tends to work better if it can read CRLs, so even an empty CRL keeps it happy. FNAL have done this for a while too.
There has been more discussion regarding the need to revoke even short lived credentials, but in general that is not yet feasible.
* Temporally suspended NGO-Netrust CA (SG)
They were suspended because of an issue with the CRL lifetime. They have a very short CRL (1 day) which can cause grid stuff to "break" because an "expired" CRL blocks everything. Another long technical discussion.
They also have some weird stuff in their certificate, like private key usage period. Sometimes the need to bring in commercial or gov't CAs, non-Grid CAs, makes it necessary for us to accept strange things in certs - but then those strange things can go on to break stuff on the grid because the grid is special.
* Withdrawn expired old PK-Grid CA (d2a353a5, superseded by f5ead794) (PK)
This is completely safe.
* Experimentally added Texas Advanced Computer Center TACC Root,
Classic, and MICS CAs to the experimental area (US)
This is interesting, I was a reviewer on the root (indeed I wrote the first set of guidelines for reviewing a root that doesn't issue end entity certs - still mean to finish that and push it through OGF.)
A "MICS" is Member Integrated Credential Service or something to that effect. The basic idea is it's fairly closely tied to a carefully maintained site database. Of course this sort of thing won't work in general out in the grid world when you have one CA per site database (again a long story), but TACC do need this sort of thing. Note it's experimental, so it's not accredited.
Eventually TACC should have two CA certs, one being a Classic and one a MICS, both tied under the same root.
Overall the release is not urgent. I meant to send out an evaluation earlier but ran out of time.
--jens
Annotated changes:
* Added accredited classic Indian Grid CA (IGCA) (hash da75f6a8) (IN)
Good for those folks over in Cambridge working on EUIndiaGrid. INFN
no longer has to be the catch all.
* Updated IUCC root certificate with extended life time (IL)
Israel: they recently went through a self audit and I need to review this audit, I've been remiss (I was assigned as a reviewer). They re-signed their certificates to extend the lifetime (previously till summer 09) and fix some bugs. It is still the same public key but the fingerprint will have changed. Unfortunately they introduced some more minor problems...
* Updated BEGrid (web, CRL) and UCSD-PRAGMA (web) URL metadata (BE, AP)
These are just the .info files.
* New BEGrid2008 root certificate (transitional) (BE)
Old one due to expire end of Feb 09, and it's still in there. Belgium may call the new one transitional(?) but its lifetime is 10 years.
Now here's the rub. If the old one expires in Feb, and the new one is created just now, what signed the existing valid certificates?
* Extended life time of the SEE-GRID CA (SEE)
Again using the same key as before, the lifetime of the existing certificates has been extended from expiring August 09 to August 2014. This is normally "harmless" except for the Mozilla NSS bug where a browser gets confused if it sees a different version of the "same" certificate at the remote end. They did in fact keep the same serial number, so they will get this problem. (Sometimes you can change the serial, sometimes not - another long story.)
"SEE" by the way is South Eastern Europe. Another EU thing. (www.see-grid.org, FP6 funded project)
* Included CRL for NCSA SLCS CA (US)
This was subject of a (yet another) long discussion. (In the world of grid certificates, long and heated is the norm for a discussion.)
The simple version is that SLCS is Short Lived Credential Service. They should not need to issue CRLs, since short lived credentials by definition live short lengths of time. However, much of the middleware tends to work better if it can read CRLs, so even an empty CRL keeps it happy. FNAL have done this for a while too.
There has been more discussion regarding the need to revoke even short lived credentials, but in general that is not yet feasible.
* Temporally suspended NGO-Netrust CA (SG)
They were suspended because of an issue with the CRL lifetime. They have a very short CRL (1 day) which can cause grid stuff to "break" because an "expired" CRL blocks everything. Another long technical discussion.
They also have some weird stuff in their certificate, like private key usage period. Sometimes the need to bring in commercial or gov't CAs, non-Grid CAs, makes it necessary for us to accept strange things in certs - but then those strange things can go on to break stuff on the grid because the grid is special.
* Withdrawn expired old PK-Grid CA (d2a353a5, superseded by f5ead794) (PK)
This is completely safe.
* Experimentally added Texas Advanced Computer Center TACC Root,
Classic, and MICS CAs to the experimental area (US)
This is interesting, I was a reviewer on the root (indeed I wrote the first set of guidelines for reviewing a root that doesn't issue end entity certs - still mean to finish that and push it through OGF.)
A "MICS" is Member Integrated Credential Service or something to that effect. The basic idea is it's fairly closely tied to a carefully maintained site database. Of course this sort of thing won't work in general out in the grid world when you have one CA per site database (again a long story), but TACC do need this sort of thing. Note it's experimental, so it's not accredited.
Eventually TACC should have two CA certs, one being a Classic and one a MICS, both tied under the same root.
Wednesday 10 December 2008
Winning hearts and minds?
(Not really operations but this is my least-inappropriate gridpp blog for this...)
I was invited by Lambeth City Learning Centre (www.lambethclc.org.uk) to give a talk about "computing and science" to schoolchildren. They were 14 year olds, it's the first time I've given talks to children.
My first main point was that increases in computing performance enables researchers in every single field of research to do more, particularly in a world where now everybody needs to collaborate. I used the grids as an example, talking about GridPP and NGS. Only one of them had heard of LHC (or would admit to it).
I used games as an analogy - they all knew those. Games visualise a world which lives inside the machine, they "collaborate" by playing with others.
The other main point I made was that they need to think. The computer is stupid, it doesn't know that it's flying a concorde, calculating the length of a bridge, or folding proteins. I gave some examples of datasets in many everyday contexts which say one thing by themselves but say something very different when you think more carefully about the data and put it in context, both historic examples and very recent ones from the news.
I definitely enjoyed giving the talk (it had been buzzing in my mind for over a month). I think they enjoyed it, too, although I was slightly worried some topics were too adult - I was also talking about computers doing epidemiology, emergency medicine, and nuclear weapons maintenance, the point being they're safer to do inside the computer than outside.
Curiously I had understood they were all girls so I had looked up quotations from women astronauts etc. What turns up on the day? Boys, every last one o'them.
I was invited by Lambeth City Learning Centre (www.lambethclc.org.uk) to give a talk about "computing and science" to schoolchildren. They were 14 year olds, it's the first time I've given talks to children.
My first main point was that increases in computing performance enables researchers in every single field of research to do more, particularly in a world where now everybody needs to collaborate. I used the grids as an example, talking about GridPP and NGS. Only one of them had heard of LHC (or would admit to it).
I used games as an analogy - they all knew those. Games visualise a world which lives inside the machine, they "collaborate" by playing with others.
The other main point I made was that they need to think. The computer is stupid, it doesn't know that it's flying a concorde, calculating the length of a bridge, or folding proteins. I gave some examples of datasets in many everyday contexts which say one thing by themselves but say something very different when you think more carefully about the data and put it in context, both historic examples and very recent ones from the news.
I definitely enjoyed giving the talk (it had been buzzing in my mind for over a month). I think they enjoyed it, too, although I was slightly worried some topics were too adult - I was also talking about computers doing epidemiology, emergency medicine, and nuclear weapons maintenance, the point being they're safer to do inside the computer than outside.
Curiously I had understood they were all girls so I had looked up quotations from women astronauts etc. What turns up on the day? Boys, every last one o'them.
Thursday 9 October 2008
September CPU efficiencies
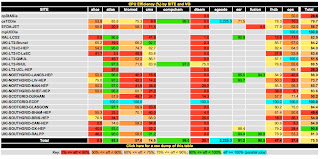
APEL data provides a view of CPU efficiencies (CPU time/Wall time) across UKI sites. The table here shows the results for September.
Monday 29 September 2008
New IGTF distribution 1.25
What's new? NCHC is back in (Taiwan), new keys not vulnerable to Debian incident. A number of metadata files were updated.
There is a new group, the IGTF RAT, Risk Assessment Team, which covers the whole world, timezone-wise (or close enough). The idea is when a vulnerability is announced via the IGTF, the RAT assesses the risk and alerts the CAs concerned. The idea, of course, comes from the Debian incident where "most" CAs had responded within a week but "most" is not good enough. So the RAT ran a test, alerting each CA to see how long it took to respond via the address advertised in the .info file. Of all currently accredited CAs, about 75% responded within 24 hours (including the UK!), but some took over a week and a second prodding. For many CAs it highlighted communications problems in their infrastructure as mail was being flagged as spam etc; these should be addressed in this release.
From a day-to-day operations point of view, you may be relieved to find the new FNAL certificate updated in the "experimental" folder, since the old one was due to expire soon.
https://dist.eugridpma.info/distribution/igtf/current/
There is a new group, the IGTF RAT, Risk Assessment Team, which covers the whole world, timezone-wise (or close enough). The idea is when a vulnerability is announced via the IGTF, the RAT assesses the risk and alerts the CAs concerned. The idea, of course, comes from the Debian incident where "most" CAs had responded within a week but "most" is not good enough. So the RAT ran a test, alerting each CA to see how long it took to respond via the address advertised in the .info file. Of all currently accredited CAs, about 75% responded within 24 hours (including the UK!), but some took over a week and a second prodding. For many CAs it highlighted communications problems in their infrastructure as mail was being flagged as spam etc; these should be addressed in this release.
From a day-to-day operations point of view, you may be relieved to find the new FNAL certificate updated in the "experimental" folder, since the old one was due to expire soon.
https://dist.eugridpma.info/distribution/igtf/current/
Tuesday 9 September 2008
All green
Subscribe to:
Posts (Atom)
